How to Build an IT Incident Response Plan

Most small businesses don’t avoid incident response planning because they think it’s unimportant. They avoid it because everything else feels more urgent—until something breaks.
Day-to-day IT already demands attention. Users need help. Systems need maintenance. Priorities shift. When things are working well enough, response planning tends to get pushed aside.
The problem is that incidents rarely arrive at a convenient time. A ransomware event, a compromised email account or even a routine issue at the wrong moment can disrupt operations faster than most teams expect.
That’s why an incident response plan matters. Not because every business needs a complex playbook, but because even a simple plan can reduce confusion, shorten downtime and help people make better decisions under pressure.
Incident response is really about reducing chaos
Most businesses do not struggle during an incident because no one cares. They struggle because too many decisions have to be made at once.
Who owns the response? Who decides what gets shut down? Who communicates—and to whom? What gets prioritized first?
Without a plan, those questions get answered in real time, often with incomplete information and increasing stress.
A good plan brings structure before that moment arrives. It creates clarity around roles, priorities and communication, so the business is not improvising when time matters most.
In the moment, that clarity allows teams to act quickly instead of debating next steps.
Start with what is most likely
The goal is not to prepare for every possible scenario. It is to prepare for the disruptions you are most likely to face.
For many businesses, that includes ransomware, email compromise, outages, hardware failures or third-party issues that affect access to systems.
The right plan is not built around technical theory. It is built around operational impact.
A simple way to approach it:
- What would stop us from serving our customers?
- What would interrupt payroll, communication or production?
- What systems need to come back first?
That is where planning becomes practical.
What should stay internal
Even with outside IT support, some parts of incident response depend on business context and need to stay internal.
- Ownership and coordination:
Someone inside the business needs to own coordination. Not to fix everything, but to keep the response moving and decisions aligned.
- Business priorities:
Only the business can define what matters most. An IT partner can restore systems, but they cannot decide what takes priority unless that is defined in advance.
- Communication expectations:
Teams should know who communicates with employees, who updates leadership and who approves external messaging. Silence creates confusion quickly.
- Critical knowledge:
Documenting key systems, vendors and recovery paths reduces risk when key people are unavailable.
Strong incident response usually comes from a combination of internal clarity and the right external support—not one or the other.
Where outside support helps
Most small businesses are not built to handle every aspect of incident response internally.
The question is: where will outside support add stability?
Over time, we often see organizations stall not because they lack awareness, but because they lack time to structure a plan. A good partner helps define roles, escalation paths and recovery priorities.
During higher-risk situations, outside expertise can support containment and determine next steps when speed matters. Monitoring also plays a key role. Many incidents become costly, simply because they are detected too late.
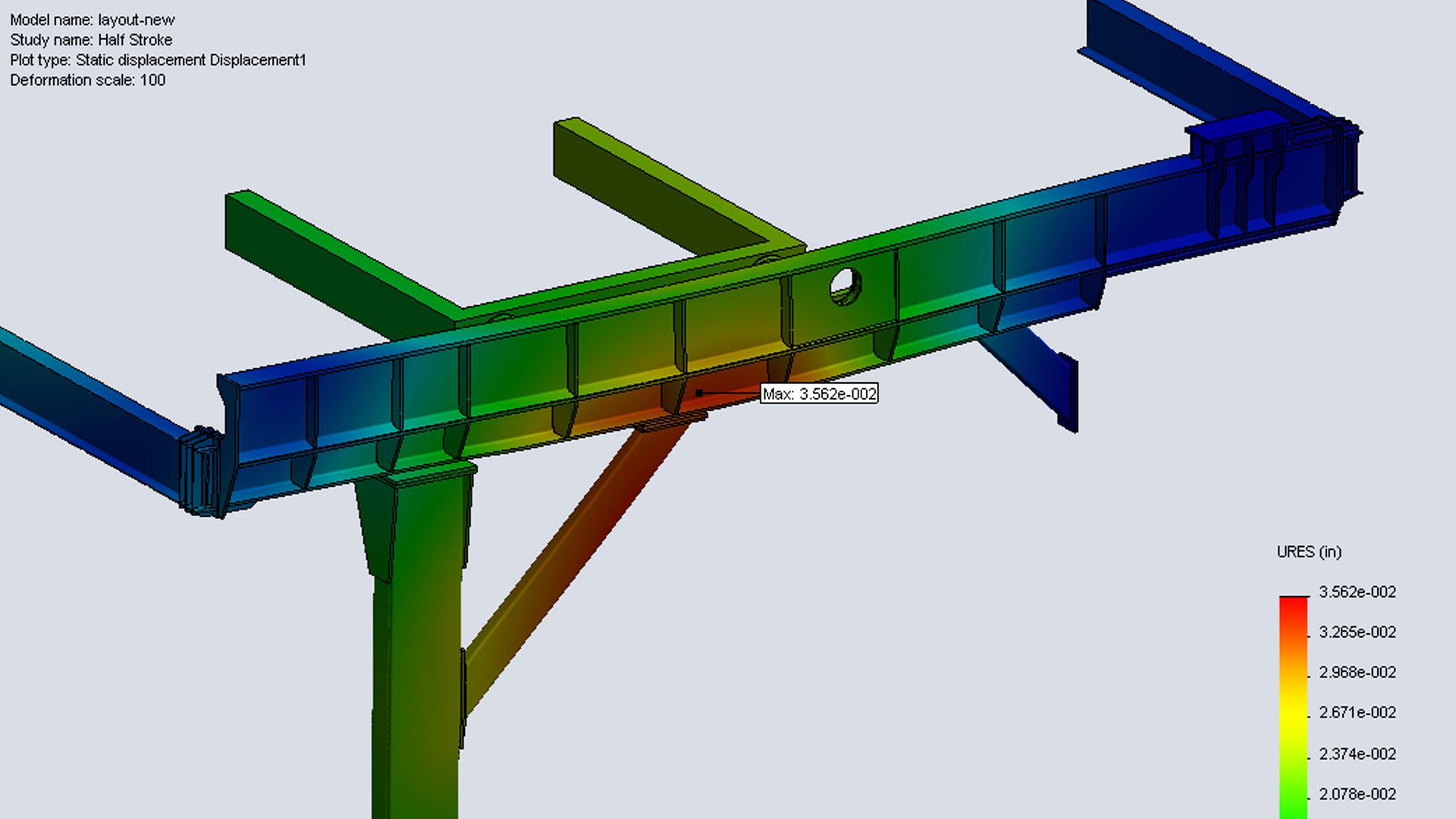
And when recovery is needed, what matters most is not just having backups—but whether systems can be restored in a timeframe that aligns with business priorities.
Keep the plan simple
One reason businesses delay planning is the assumption that it needs to be extensive. It does not.
A useful plan can start with a few essentials: what you are planning for, who owns the response, who to contact and what systems matter most.
Just as important are the first actions—what happens immediately after an incident, and how communication will work during a disruption. That is enough to move from reactive to prepared.
Train for clarity, not drama
Incident response training does not need to be complex. Simple discussions are often enough.
Walk through a scenario. Who gets called? What gets shut down? How does the team operate if a core system is unavailable?
These conversations usually reveal the same thing: people assume someone else owns more of the response than they actually do. That is exactly why this exercise matters.
What this really creates
The goal is not to eliminate every disruption. No plan can do that.
The goal is to create a more stable response when something does go wrong.
That means less confusion, clearer ownership, faster escalation and shorter downtime.
For small businesses, that kind of predictability is what turns disruption into something manageable instead of something chaotic.
If you are not sure who would own the response or what would happen first during an incident, that is usually a sign the plan has not been clearly defined yet.
That uncertainty is normal. The important step is turning it into clarity.
Seifert Technologies is always happy to serve as a resource, whether that means answering questions or helping you think through a practical plan. Call 330.833.2700 ext. 113 or email sales@seifert.com to start building your incident response plan today.
FAQs About IT Incident Response Plans
What is an IT incident response plan?
An incident response plan outlines how your business responds to outages, security events and other disruptions.
Why does a small business need one?
Small businesses often have less redundancy, so confusion and downtime can escalate quickly without clear roles and next steps.
What incidents should be included?
Ransomware, email compromise, outages, hardware failures and disruptions that affect core operations.
What should stay internal?
Ownership, priorities, communication decisions and knowledge of critical workflows.
When should outside support be involved?
For planning, monitoring, recovery testing, security incidents and coordination with vendors or insurers.
How often should it be reviewed?
When systems or responsibilities change, with an annual review as a practical baseline.